Cybersecurity Law Is A Dynamic Landscape
We Aim To Provide Clients With Clarity
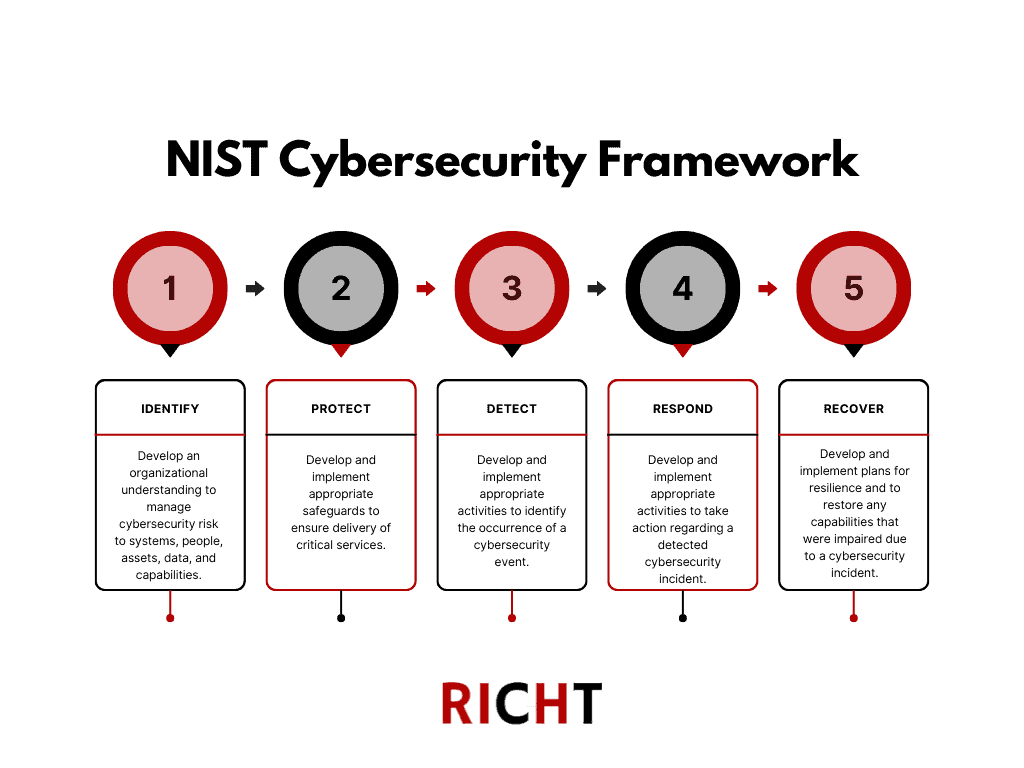
In our increasingly data-first world, cybersecurity is more critical than ever in guarding against cyberattacks that can be catastrophic. In light of the ever-expanding and critical nature of cybersecurity, laws of cybersecurity are dynamic and growing, with several laws in effect, ranging from the EU and UK versions of the GDPR, US state-specific laws such as California’s CCPA as amended by the CPRA and New York’s SHIELD Act and the NYDFS cybersecurity regulation, as well as sector-specific laws such as HIPAA for health information, to the GLBA for financial data, and the SEC’s cybersecurity breach disclosure rules. Layered on top of these laws are cybersecurity frameworks and standards, such as those from the NIST, as well as regulatory guidance, including the UK’s National Cyber Security Centre (NCSC) guide to CEOs on cyber incident response. Furthermore, with the proliferation of artificial intelligence, cybersecurity regulations and standards are becoming increasingly prominent.
While many of these laws have a privacy-specific focus, such as how data can be processed, they also have cybersecurity components, such as the kinds of security needed to ensure the safety and integrity of information to the required procedures that must be followed in the event of a data breach, including regulator and consumer notification. While larger businesses operating globally have larger risk vectors in the cybersecurity context, even smaller businesses must contend with cybersecurity and, by extension, cyberattacks.
Some examples of cybersecurity, privacy, and related data protection laws having an impact on companies, including via enforcement actions, include the following:
- Irish Data Protection Commission fines Meta Ireland €91 million: The Data Protection Commission (DPC) has today announced its final decision following an inquiry into Meta Platforms Ireland Limited (MPIL). This inquiry was launched in April 2019, after MPIL notified the DPC that it had inadvertently stored certain passwords of social media users in ‘plaintext’ on its internal systems (i.e., without cryptographic protection or encryption).
- Marriott agrees to pay $52 million, beef up data security to resolve probes over data breaches: Marriott International has agreed to pay $52 million and make changes to bolster its data security to resolve state and federal claims related to major data breaches that affected more than 300 million of its customers worldwide.
At RICHT, we recognize the importance of having a cybersecurity lawyer to advise businesses on navigating today’s digital and dynamic regulatory frameworks, alongside an ever-evolving threat landscape. We focus on helping clients avoid costly legal cybersecurity risks and mitigate damage from cybersecurity incidents and matters that may arise. Whether it is incident and breach response and notification to data privacy and protection, we work closely with our clients to develop tailored strategies that meet their unique needs. In addition, in conjunction with RICHT&Co., we offer a range of technical services, including vulnerability assessments and penetration testing, to help our clients identify and address potential security vulnerabilities before they can be exploited. In addition, clients benefit from reputational risk management and PR strategy via Baker Hartford.
Cybersecurity Law Services We Offer
Some Of The Types Of Clients We Can Help